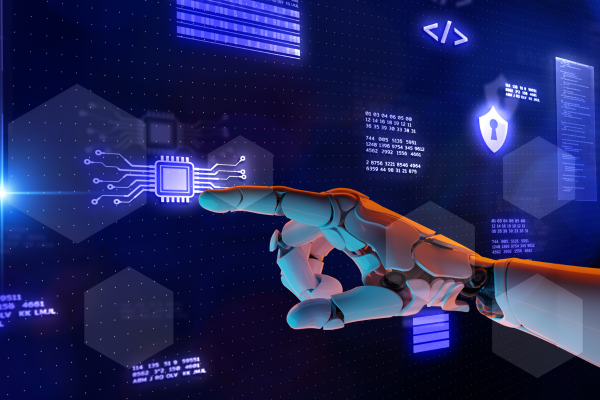
Preparation is paramount for many companies as States and Territories slowly ease up on their lockdowns, and none is more important than maintaining information resilience by managing cybersecurity risks and data privacy regulations.
Organizations are currently reviewing their guidelines such as planning one-way systems, implementing staggered start and finish times, reviewing the effectiveness of safety controls and measures, and taking immediate action to improve those that are not effective.
From a cybersecurity perspective, this includes reassessing system networks, reviewing Shadow ITˡ activity, or bring your own device (BYOD) usage. While for data protection, the focus will be on workstation changes, employee health data, data protection impact assessments (DPIAs) and transparency.
Focused on supporting companies across all industry sectors in planning their reopening and developing a sustainable methodology, business improvement company BSI has outlined ten cybersecurity and data protection essentials that should be considered:
- Physical security – organisations should make sure that their physical security controls, employee identification and physical media are all up to date and fully operable.
- Access control – credentials such as multi-factor authentication (MFA) and password expiration and reset should all be up to date.
- Data protection and privacy – companies should also seek the advice of the Data Protection Officer or Privacy Officer on the impact of changes made to existing processes or new processes where data is recorded and collated. Also, Privacy Impact Assessments (PIAs) should be conducted wherever relevant.
- Asset management – Bring Your Own Device (BYOD) policies should be re-evaluated to ensure that all non-inventoried assets are correctly logged.
- Network security – remote access is still important during a phased return to work, network services such as Virtual Private Networks (VPNs) should be kept available and secure.
- Vulnerability management – with patching being a challenge even for an information resilient organization, organisations must evaluate their patch posture and where to prioritize patching in their systems to prevent any hacks.
- Operations security – organisations should re-evaluate any configurations they made during the WFH period to ensure that they are still the most effective.
- Business continuity – companies should also learn from their recent activities – the remote working paradigm – and apply the acquired knowledge to improve the readiness of the business continuity plan.
- Incident management – incident response represents the last line of defence should an attack materialize, so organizations should create a set up in preparing for and responding to a data breach.
- Security governance – risk registers should be reassessed given the newly restructured threat landscape and control plane.
BSI has developed a self-assessment questionnaire for organizations that measures their readiness to reopen based on their cybersecurity and data governance implications. This questionnaire is accessible on their website.
“The last few months have tested many organizations of all shapes and sizes across the globe. Many needed to adapt quickly to the restrictions to ensure the safety and wellbeing of their employees and clients, with remote working being activated, and IT systems tested and reconfigured to remain effective,” BSI’s Global Practice Director for Cyber, Risk and Advisory Stephen O’Boyle said.
“While there were many challenges, including the increase in cyber threats and risks, and data privacy concerns, it also provided organizations with the opportunity to customize, review, update and improve their response planning and enhance their business continuity plans to prepare for the phased reopening.”
Director O’Boyle stated that an organization should be focused on opening safely by listening to its cybersecurity and data governance needs. He also stated that those responsible for the safety during the transition should also be part of the planning process to ensure strict adherence to protocols.
With these in mind, organisations will be able to operate in a more secure, safe, sustainable, trusted, and resilient manner, protecting their people, information and reputation.
Pearl Dy is a community manager and journalist. She is passionate about business and development particularly involving digital economy, not-for-profits, charity and social entrepreneurship.