Bosch Rexroth Nutrunner vulnerabilities disrupt production
Share
Nozomi Networks has detailed new vulnerabilities discovered in the Bosch Rexroth NXA015S-36V-B, a popular smart nutrunner (pneumatic torque wrench) used in automotive production lines. We demonstrate that these vulnerabilities could make it possible to implant ransomware on the device, which could be used to cause production line stoppages and potentially large-scale financial losses to asset owners. Another exploitation would allow the threat actor to hijack tightening programmes while manipulating the onboard display, causing undetectable damage to the product being assembled or making it unsafe to use. Given that the NXA015S-36V-B is certified for safety-critical tasks, an attacker could compromise the safety of the assembled product by inducing suboptimal tightening or causing damage to it due to excessive tightening.
In critical applications, the final torque levels applied to mechanical fastenings are calculated and engineered to ensure that the overall design and operational performance of the device are met. As an example, bolts, nuts, and fixtures used in electrical switchboards must be torqued appropriately to ensure that connections between current-carrying components, such as high-voltage busbars, maintain low resistance. A loose connection would result in higher operating temperatures and could, over time, cause a fire.
As these vulnerabilities, primarily in the NEXO-OS operating system, have yet to be patched, we will not reveal any technical details. Bosch Rexroth has committed to releasing patches by the end of January 2024. In the interim, this report contains some mitigations that asset owners can implement to safeguard against cyberattacks.
The Bosch Rexroth NXA015S-36V-B and NEXO-OS
The NXA015S-36V-B is a cordless, handheld pneumatic torque wrench (nutrunner) in the Bosch Rexroth NXA Angle Head family. It is specifically engineered for safety-critical tightening operations falling under category A of VDI 2862, a standard established by the Association of German Engineers (VDI) and adopted by the automotive industry in 1999.
The nutrunner is equipped with a visual display presenting real-time data and activity results to the operator. Additionally, it can connect to a wireless network through its embedded Wi-Fi module. In this configuration, data can be transmitted using various supported protocols to a designated historian server, and the device can be remotely reprogrammed using the management services provided by its NEXO-OS operating system.
NEXO-OS serves as the Linux-based operating system powering the nutrunner. It presents a range of application choices, encompassing tightening system configuration, the generation of tightening programmes by specifying processes, and the analysis and diagnosis of tightening cases through the exposed management web application. It also supports a wide range of communication protocols, such as Rexroth OpenProtocol, VW-XML, and BMW-TPC, so that the nutrunner can be seamlessly integrated with SCADA systems, PLCs, or other production devices.
The majority of the vulnerabilities identified by Nozomi Networks Labs affected the management web application, although a few were found in the services parsing the mentioned protocols. In the next section, we outline the key impacts that could result from the exploitation of these flaws. The full list of vulnerabilities can be found immediately after it.
What Are the Impacts of These Vulnerabilities?
The vulnerabilities found on the Bosch Rexroth NXA015S-36V-B allow an unauthenticated attacker who can send network packets to the target device to obtain remote execution of arbitrary code (RCE) with root privileges, completely compromising it. Once this unauthorised access is gained, numerous attack scenarios become possible. Within our lab environment, we successfully reconstructed the following two scenarios:
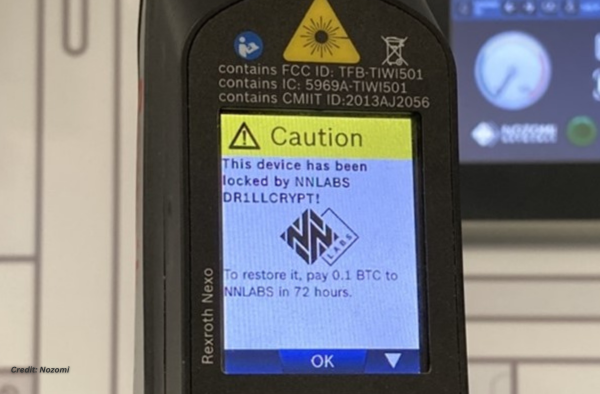
Ransomware: We were able to make the device completely inoperable by preventing a local operator from controlling the drill through the onboard display and disabling the trigger button. Furthermore, we could alter the graphical user interface (GUI) to display an arbitrary message on the screen, requesting the payment of a ransom. Given the ease with which this attack can be automated across numerous devices, an attacker could swiftly render all tools on a production line inaccessible, potentially causing significant disruptions to the final asset owner.
Manipulation of Control and View: We managed to stealthily alter the configuration of tightening programmes, such as by increasing or decreasing the target torque value. At the same time, by patching in-memory the GUI on the onboard display, we could show a normal value to the operator, who would remain completely unaware of the change.
Aside from the potential health and safety risks that may arise from improperly torqued fastenings in critical devices, the potential for business harm extends to other types of losses.
An overtightened connection places excess stress on the bolt and nut, which, again over time, will cause premature failure of the fixture, possibly through failure of the threads themselves or possibly exceeding the elastic limits of the material, resulting in deformation. As the fixture stretches or the threads fail, the connection integrity is compromised, again resulting in a loose connection. These types of mechanical failures cause not only loss of revenue and productivity to the end user and customer but are likely to result in excessive warranty claims and reputational damage to your business and could amount to a significant financial risk or loss over an extended period of time.
Depending on a manufacturer’s use and business configuration, devices such as the nutrunner may form a critical part of the quality management and assurance programme in an enterprise, possibly even the last line of quality assurance. The compromise of integrity in this final link in the quality chain may be difficult to detect and have far-reaching financial consequences resulting from compromised production quality over time.
Vulnerability Spotlight
There are diverse methods through which an attacker could potentially execute root-level code on the device. For example, take the web management interface, which is always exposed on the network. With a valid account, even with the least available privileges, exploiting issues like path traversal in file upload (CVE-2023-48243) would be adequate to achieve the target. An unauthenticated attacker might still succeed by chaining this with the exploitation of other issues to initially gain valid authenticated access to the device, such as the abuse of one of the hardcoded accounts (CVE-2023-48250).
Additionally, if any of the communication protocols for integration with other systems (e.g., OpenProtocol) are enabled, exploiting the device becomes as simple as abusing just one of the identified buffer overflow vulnerabilities (such as CVE-2023-48265), as they all can be triggered without providing authentication details.
Today, a wide variety of vulnerabilities are discovered every day, and it is safe to say that most attacks, especially in OT and IoT environments, don’t reach the entire potential damage, not because of the lack of access and unauthorised control, but only because the hacker itself doesn’t know how to use the devices they are breaking into. Nonetheless, it is extremely important to always be aware and proactive in anticipating these vulnerabilities because their potential damage, as we demonstrated, is undoubtedly devastating.
Remediations
Bosch Rexroth is set to deliver official patches by the end of January 2024. In the meantime, we advise adopting the following mitigations to protect against cyberattacks:
Given that some vulnerabilities are zero-click unauthenticated root RCE, we recommend restricting the network reachability of the device as much as possible so that only authorised personnel and trusted computers or servers can communicate with it.
As some vulnerabilities can be exploited by authenticated users only, we suggest reviewing all accounts that have login access to the device and deleting unnecessary ones.
Finally, a few vulnerabilities require authenticated users to click on links or visit malicious webpages while logged in to the management web application. To counteract these, we advise being cautious when opening untrusted links or visiting external websites with a browsing session on the management web application in progress.
Conclusion
While two general attack examples are discussed here, it is worth the effort to assess the potential impact of any of these attacks on your organisation and technologies, either applied alone or in combination.
A group of malicious hackers might render an assembly line unusable if you don’t pay a fortune in cryptocurrency to the threat group. A resulting ransom demand may be millions of dollars before considering the remediation and response costs. Finally, availability and quality disruptions could result in reputational damage, especially if an organisation is unprepared for downtime or a product is unavailable for an extended period of time.
Long-term, unmitigated alteration could affect product quality, forcing you to recall thousands of products already on the market. A threat group or individual might reach out to you, revealing a potential flaw in the manufacturing process, but not give the entire details until you pay for it. The implications are extensive, from potentially dangerous accidents to complex lawsuits derived from defective product operations and the potential for ransomware—the sky is the limit when it comes to potential impacts.
Fortunately, vulnerabilities have been researched and disclosed by our team, and we are working together with the manufacturer to provide timely information and collaborate in the delivery of patches to the public.

Justin Lavadia is a content producer and editor at Public Spectrum with a diverse writing background spanning various niches and formats. With a wealth of experience, he brings clarity and concise communication to digital content. His expertise lies in crafting engaging content and delivering impactful narratives that resonate with readers.


Today’s Pick
11th Annual Aus Goverment Data Summit
April 1, 2025
7th Annual NZ Government Data Summit
May 7, 2025
3rd Public Sector Comms Week
May 14, 2025
Subscribe
We send emails,
but we do not spam
Join our mailing list to be on the front lines of healthcare , get exclusive content, and promos.
AI appointment Australia Australian boost boosts business businesses covid-19 cyber cyber attack cyber security cybersecurity data data breach data management defence Digital employment enhance enhances fraud funding governance government grants infrastructure Innovation Lockdown management new zealand NSW NZ online privacy public Public Sector queensland renewable energy scams security Social Media Technology telecommunications victoria
-

Understanding and building your digital strategy
Digital Government, Opinion
-

Featured Leader: Jamie Morse on multi-channel strategies for communication
Communications, Featured Leader
-

Featured Leader: Tegan Tembe of NSW Treasury on creating solid planning strategies and processes
Featured Leader
-

Wirraka Maya Health Service improves patient care with My Health Record
Learning
Show More-

Effects of ineffective communication in the workplace
Communications, Personal Development
-

7 ways you can enhance your personal development skills
News, Personal Development
-

5 advantages of working in the public sector
News, Personal Development, Professional Development
-

7 causes of communication issues in the workplace
Communications, News, Personal Development
Show MoreLast Viewed
WA Government adopts cloud-based system for grant application
Australian Gov enacts new measures to help flood-affected communities
Liberal and National Government invests $1.3B in telecommunications
Victorian Government launches $2.2M initiative to support Agtech
Featured Leader: Ken Maxwell of xAmplify on government using digital services