Recent data breaches have highlighted the importance of strong cybersecurity measures for Australian businesses, emphasising the increased risks and challenges they face in safeguarding sensitive information. As cyber threats rise, it becomes increasingly clear that strict safeguards are necessary. The importance of these breaches stems from their ability to potentially expose sensitive information, which can put business operations and customer trust at risk.
Surge in data breaches
There has been a significant increase in data breaches in Australia, with a particular focus on the financial and healthcare sectors. In the year 2020, there has been a notable increase in data breaches, with a total of 2,784 incidents reported by the Office of the Australian Information Commissioner (OAIC). These breaches have infiltrated different sectors, revealing weaknesses across industries and underscoring the widespread presence of cyber threats in the Australian business landscape.
In the second half of 2022, the Office of the Australian Information Commissioner (OAIC) reported a significant increase in breaches. These breaches have had a widespread impact, affecting the personal information of millions of Australians. Criminal attacks and human error have contributed to the increase in breaches.
In the latter half of 2023, the OAIC documented 38 data breaches that had a significant impact on government agencies. This marks a notable shift as government agencies have returned to the ‘top five’ sectors in terms of breach numbers, a position they haven’t held in nearly three years. The scale and frequency of these breaches indicate the urgent need for strong cybersecurity measures and proactive risk management strategies within Australian businesses.
Significant Australian data breaches
There has been a notable increase in data breaches in Australia, with two major incidents recently affecting businesses. In May 2019, Canva, an Australian tech company, experienced a significant data breach that impacted 137 million users. The security breach resulted in the exposure of highly sensitive information, such as usernames, real names, and email addresses. In March 2023, Latitude, a financial service provider, faced a major breach of privacy that affected more than 14 million individuals in Australia and New Zealand.
An extensive data breach has resulted in the exposure of highly sensitive information, encompassing individuals’ complete names, residential addresses, contact numbers, dates of birth, driver’s licence details, and passport numbers. In addition to these well-known cases, there have been significant security breaches that have made an impact on the Australian business scene, indicating the need for strong cybersecurity measures.
An example of a cyberattack. This attack had an extensive effect on a large number of customers, as it compromised their sensitive information and undermined their confidence in the security of digital transactions. In addition, the Blackbaud data breach has had major consequences for numerous organisations, indicating the extensive repercussions of cyber attacks and the urgent need for increased vigilance.
Australia’s cybersecurity roadmap
The Australian government is taking proactive measures to address the increasing cybersecurity threats by undertaking a thorough review of its frameworks and policies. By 2030, the government aims to establish itself as a global powerhouse in the field of cybersecurity. To achieve this, the government has developed a roadmap known as the 2023–2030 Australian Cyber Security Strategy. Six crucial areas, known as “cyber shields,” centre the strategy.
These variables include strong businesses and individuals, secure technology, effective sharing and prevention of threats, protected critical infrastructure, national capabilities, resilient regions, and international prominence. Every shield enhances the level of protection against cyber threats and prioritises the well-being of Australian citizens and businesses. To ensure the safety of the nation, the government is taking a comprehensive approach to cybersecurity, prioritising support for civilians and industry.
Its primary goal is to address and take concrete steps towards resolving the cybersecurity concerns that are of utmost importance to Australian communities and businesses. Nevertheless, these government initiatives merely elevate the standard level of security. It is key for every business to uphold and enhance their data breach prevention controls. This approach illustrates the significance of collaborations between the public and private sectors in strengthening Australia’s cybersecurity resilience.
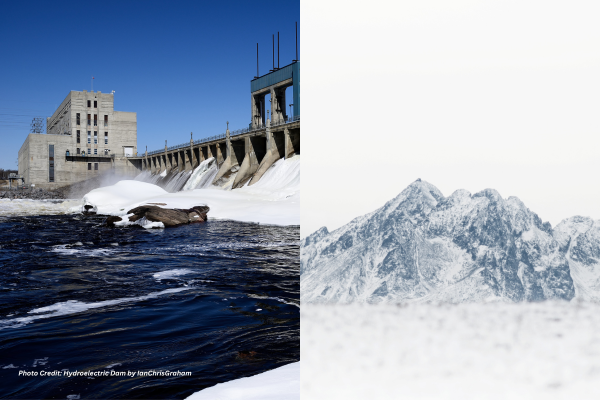
Global supply chain cyber risks
Supply chains present notable cybersecurity risks due to their interconnected nature. The risks arise from the intricate and interconnected system that involves the design, manufacturing, distribution, deployment, use, maintenance, and management of products and services on a global scale. There are several potential risks that businesses need to be aware of.
These threats can include the presence of counterfeit products, unauthorised production, tampering, theft, and the introduction of malicious software and hardware. Inadequate manufacturing and development practices in the cybersecurity-related aspects of the supply chain further exacerbate these risks. Due to the numerous sources of components and software typically used in a final product, the global supply chain exposes companies and consumers to cybersecurity threats.
An international collaboration may have been involved in the creation of a device, with different components sourced from various locations across the globe. Different companies may have assembled these components. In order to effectively address these risks, organisations must prioritise the maintenance of the supply chain’s integrity, security, quality, and resilience. One important aspect is to analyse, evaluate, and minimise the potential risks that arise from the widespread and interconnected nature of ICT/OT product and service supply chains.
Data breach financial impact
Data breaches heavily impact businesses and their financial burden. Over the past five years, the cost of a data breach has increased significantly by 12%, reaching an average of $3.92 million. Small and midsize businesses bear a significant burden when it comes to this expense, as those with fewer than 500 employees experience losses exceeding $2.5 million. The expenses incurred extend beyond the immediate aftermath of a security breach. The majority of data breach costs, approximately 67%, accumulate within the first year following a breach.
Another 22% of costs accrue in the second year, with an additional 11% occurring more than two years after the breach. Long-term costs may arise, such as a potential loss of competitive advantage, a decrease in credit rating, and higher cyber insurance premiums. The financial sector is at high risk, as data breaches can be extremely costly, with an average cost of $5.72 million in 20213. These costs underscore the importance of businesses investing in cybersecurity and resilience-building initiatives.
Businesses in Australia should not overlook the significant financial impact that data breaches have. The increasing costs associated with data breaches, along with the potential for legal consequences, regulatory penalties, and damage to one’s reputation, underscore the importance of implementing strong preventive measures. In addition, failure to comply with data protection regulations can result in significant penalties, placing an additional financial burden on affected organisations.
Australian businesses face a multitude of new challenges in the ever-changing world of cybersecurity threats. In order to overcome these obstacles, businesses need to stay alert and adjust their cybersecurity strategies accordingly. Staying up-to-date on emerging threats and investing in the latest technologies and best practices can help businesses reduce the risks of data breaches and protect their financial stability and reputation in today’s digital landscape.
Justin Lavadia is a content producer and editor at Public Spectrum with a diverse writing background spanning various niches and formats. With a wealth of experience, he brings clarity and concise communication to digital content. His expertise lies in crafting engaging content and delivering impactful narratives that resonate with readers.